Google Drive’s Ransomware Shield: A Glimpse into Proactive Data Security
Nearly 40% of organizations experienced a ransomware attack in the last year, a figure that’s not just alarming, but accelerating. Now, Google is taking a significant step towards preemptive defense with its new ransomware detection and recovery features in Drive. But this isn’t simply a reactive patch; it’s a harbinger of a future where cloud storage isn’t just about *storing* data, but actively *protecting* it from evolving threats.
Beyond Detection: The Rise of Predictive Security
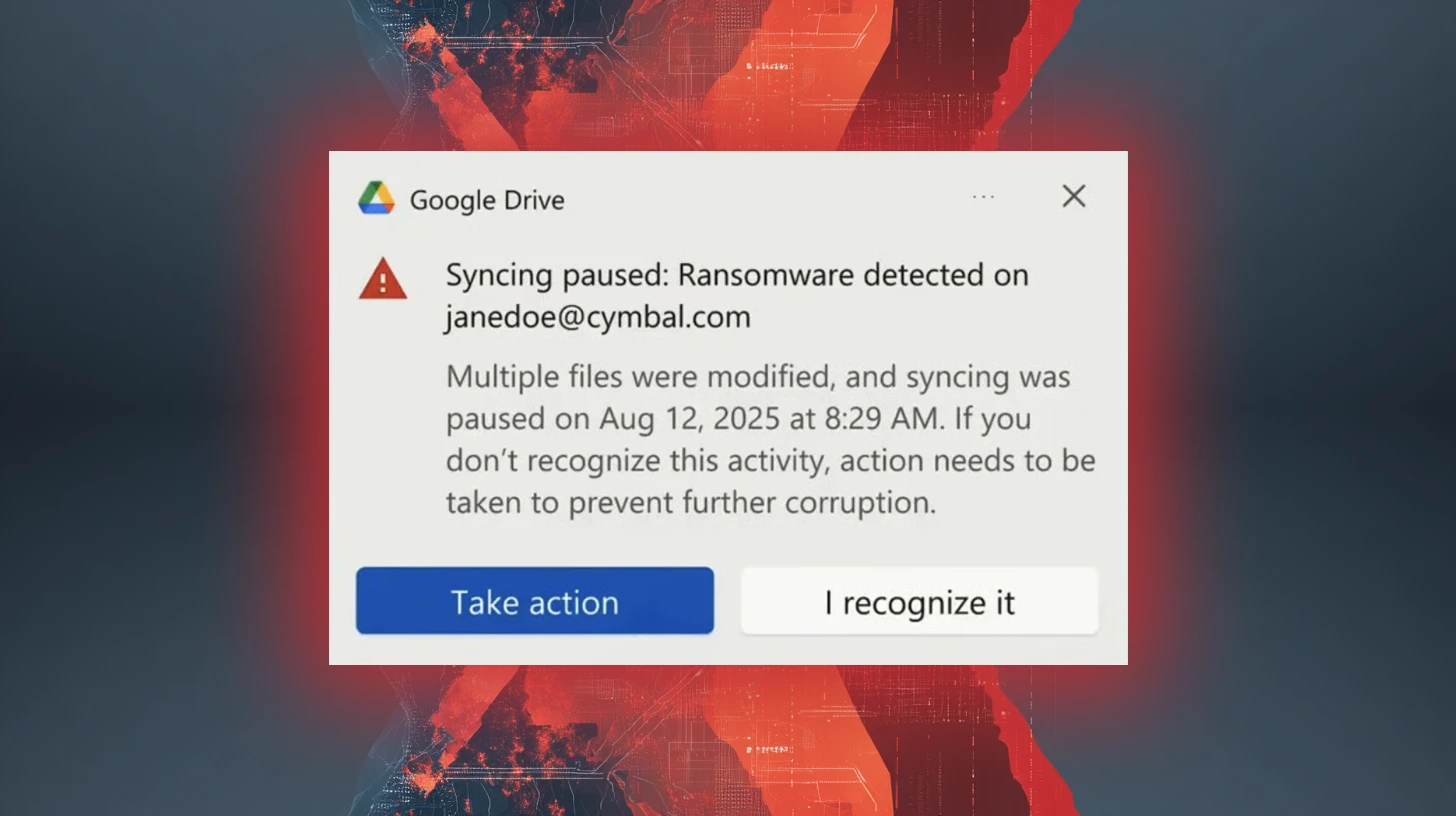
Google’s latest update for Drive desktop now scans uploaded files for signs of ransomware, leveraging behavioral analysis to identify malicious code. This is a crucial improvement over traditional signature-based detection, which often lags behind new threats. However, the real game-changer lies in the potential for this technology to evolve into predictive security. Imagine a future where Drive doesn’t just react to ransomware, but anticipates it, blocking malicious uploads *before* they can encrypt your files.
This shift is driven by advancements in machine learning and artificial intelligence. By analyzing file patterns, user behavior, and threat intelligence feeds, cloud storage providers can identify anomalies that suggest a potential attack. This proactive approach is becoming increasingly vital as ransomware attacks become more sophisticated and targeted.
The Recovery Advantage: Version History as a Lifeline
Detection is only half the battle. Google Drive’s robust version history feature is now a critical component of its ransomware recovery strategy. By automatically preserving previous versions of files, Drive allows users to revert to a clean state before the encryption occurred. This is a significant advantage over traditional backup solutions, which can be time-consuming to restore and may not always capture the most recent versions of files.
However, relying solely on version history isn’t foolproof. Attackers are increasingly employing techniques like “slow and low” attacks, where encryption occurs gradually over time, making it harder to detect. This highlights the need for a multi-layered security approach that combines proactive detection with robust recovery mechanisms.
The Expanding Role of Cloud Providers in Cybersecurity
Google’s move signals a broader trend: cloud providers are assuming a more active role in cybersecurity. Historically, security was largely the responsibility of the end-user. But as data breaches become more frequent and costly, cloud providers are recognizing the need to offer built-in security features that protect their customers. This is particularly important for small and medium-sized businesses (SMBs) that may lack the resources to implement and maintain sophisticated security solutions.
We’re likely to see other cloud storage providers follow suit, offering similar ransomware detection and recovery features. This will lead to a “security arms race,” where providers constantly innovate to stay ahead of evolving threats. The ultimate beneficiary will be the end-user, who will benefit from a more secure and resilient cloud environment.
| Feature | Traditional Backup | Google Drive Ransomware Protection |
|---|---|---|
| Detection | Reactive (signature-based) | Proactive (behavioral analysis) |
| Recovery Time | Hours/Days | Minutes/Hours (version history) |
| Complexity | High (manual configuration) | Low (automatic, built-in) |
The Future of Data Security: Zero Trust and Beyond
Looking ahead, the future of data security will be defined by the principles of Zero Trust. This security model assumes that no user or device is inherently trustworthy, and requires continuous verification before granting access to data. Cloud storage providers will play a key role in implementing Zero Trust architectures, offering features like multi-factor authentication, granular access controls, and continuous monitoring.
Furthermore, we can expect to see increased integration between cloud storage and other security tools, such as endpoint detection and response (EDR) systems. This will allow for a more holistic and coordinated security posture, enabling organizations to detect and respond to threats more effectively. The evolution of quantum computing also presents a long-term challenge, requiring the development of quantum-resistant encryption algorithms to protect data from future attacks.
Frequently Asked Questions About Ransomware Protection in Cloud Storage
<h3>What is behavioral analysis and how does it help detect ransomware?</h3>
<p>Behavioral analysis examines how files behave, looking for suspicious activities like rapid encryption or modification of system files. This allows detection of new ransomware variants that haven't been identified by traditional signature-based methods.</p>
<h3>Is Google Drive’s version history a sufficient backup solution?</h3>
<p>While version history is a valuable recovery tool, it shouldn’t be your only backup strategy. A comprehensive backup plan should include offsite backups and regular testing of recovery procedures.</p>
<h3>What is Zero Trust security and how will it impact cloud storage?</h3>
<p>Zero Trust assumes no user or device is trustworthy and requires continuous verification. In cloud storage, this means stronger authentication, granular access controls, and constant monitoring of user activity.</p>
<h3>How can I further protect my data in Google Drive?</h3>
<p>Enable two-factor authentication, use strong passwords, be cautious of suspicious links and attachments, and regularly review your sharing permissions.</p>The advancements Google is making with Drive are indicative of a fundamental shift in how we approach data security. It’s no longer enough to simply react to threats; we must proactively defend against them. As cloud storage becomes increasingly central to our digital lives, the security of our data will depend on the ability of providers to anticipate and neutralize evolving threats.
What are your predictions for the future of ransomware protection in cloud storage? Share your insights in the comments below!
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.