The Airport Hack is a Warning: The Coming Era of Targeted Infrastructure Disruption
Over 800 million cyberattacks were detected globally in the first half of 2023 alone. But the recent coordinated breaches at airports in Toronto, Atlanta, Las Vegas, and Chicago – where PA systems were hijacked to broadcast politically charged messages – represent a chilling evolution. This wasn’t about stealing data; it was about exploiting vulnerabilities to directly manipulate public perception and demonstrate the potential for widespread disruption. This incident isn’t an isolated event; it’s a harbinger of a future where critical infrastructure is increasingly targeted for information warfare.
Beyond the Headlines: Understanding the New Threat Landscape
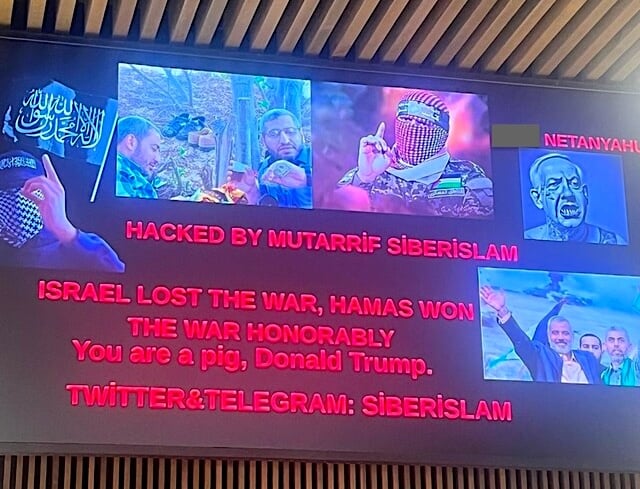
The immediate fallout from the airport hacks involved swift responses from authorities and assurances that flight operations weren’t compromised. However, focusing solely on the lack of operational impact misses the larger point. The hackers didn’t aim to ground planes; they aimed to sow discord and test the resilience of our public spaces. The messages, ranging from pro-Hamas statements to anti-Trump rhetoric, were deliberately provocative, designed to maximize media coverage and psychological impact.
This attack differs significantly from traditional cybercrime. While ransomware attacks aim for financial gain, this was a demonstration of capability – a proof of concept for a new form of hybrid warfare. The ease with which the hackers gained access to the PA systems, reportedly through compromised third-party vendors, highlights a critical weakness in airport security protocols. Many airports rely on interconnected systems managed by external companies, creating a complex web of potential vulnerabilities.
The Rise of “Operational Technology” (OT) as a Prime Target
Airports, power grids, water treatment facilities – these are all examples of systems controlled by Operational Technology (OT). Unlike Information Technology (IT), which deals with data processing, OT controls physical processes. Historically, OT systems were isolated from the internet, making them relatively secure. However, the increasing adoption of IoT devices and cloud-based management solutions has blurred the lines between IT and OT, creating new attack vectors.
Why OT is More Vulnerable
OT systems often run on outdated software and lack the robust security measures found in modern IT infrastructure. They were built for reliability, not security. Furthermore, the consequences of a successful attack on OT systems can be far more severe than a data breach. Imagine a coordinated attack on multiple power grids, or a disruption to air traffic control systems. The potential for chaos and loss of life is immense.
The airport hack serves as a stark reminder that these vulnerabilities are real and exploitable. It’s no longer a question of *if* OT systems will be targeted, but *when* and *how*.
| Vulnerability | Risk Level | Mitigation Strategy |
|---|---|---|
| Third-Party Vendor Access | High | Rigorous vendor security assessments, multi-factor authentication, and limited access privileges. |
| Outdated OT Software | High | Regular software updates, patching vulnerabilities, and system segmentation. |
| Lack of Network Segmentation | Medium | Isolate OT networks from IT networks, implement firewalls, and monitor network traffic. |
The Future of Airport Security: A Multi-Layered Approach
Addressing this evolving threat requires a fundamental shift in how we approach airport security – and the security of all critical infrastructure. Traditional cybersecurity measures are no longer sufficient. A multi-layered approach is needed, encompassing:
- Enhanced Threat Intelligence: Proactive monitoring of threat actors and their tactics, techniques, and procedures (TTPs).
- Zero Trust Architecture: Assuming that no user or device is trustworthy, and verifying every access request.
- Resilience Planning: Developing contingency plans for responding to and recovering from cyberattacks.
- Public-Private Partnerships: Collaboration between government agencies, airport operators, and cybersecurity firms.
- AI-Powered Security: Utilizing artificial intelligence and machine learning to detect and respond to anomalies in real-time.
The incident at the airports wasn’t just a hack; it was a wake-up call. It demonstrated the potential for adversaries to exploit vulnerabilities in our critical infrastructure to achieve strategic objectives. The era of passively defending our systems is over. We must proactively anticipate and prepare for the next wave of attacks.
What are your predictions for the future of airport and critical infrastructure security? Share your insights in the comments below!
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.