From Manual Drudgery to Digital Precision: How UTMStack is Revolutionizing Compliance Automation
WASHINGTON — For too long, organizational compliance has been a game of “catch-up,” where security teams spend more time filling out spreadsheets than actually securing their networks. The industry is reaching a breaking point as regulatory frameworks grow in complexity, turning the annual audit into a dreaded resource drain.
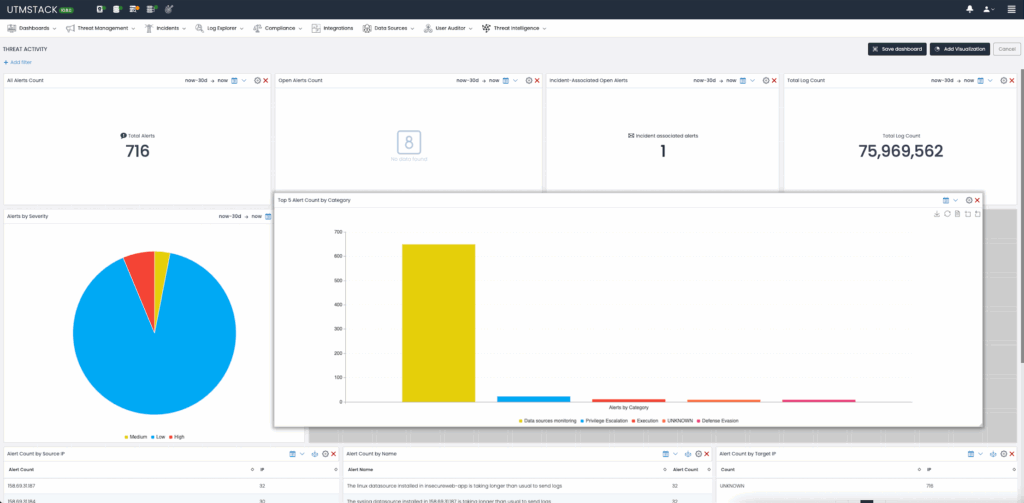
Enter UTMStack. By integrating an open-source Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) architecture, the platform is shifting the paradigm toward compliance automation.
The mission is clear: stop the manual hunt for evidence and replace it with a continuous, living stream of validation. By leveraging log centralization and automated correlation, UTMStack is effectively turning the “audit” from a snapshot in time into a real-time heartbeat.
The High Cost of Manual Compliance
Frameworks such as GDPR, HIPAA, PCI DSS, and SOC2 are not mere suggestions; they are rigorous mandates requiring constant monitoring and meticulous documentation.
When organizations manage these security controls manually, they often succumb to “compliance fatigue.” This exhaustion redirects critical talent away from strategic growth and toward the tedious collection of logs and screenshots.
Is your team spending more time proving they are secure than actually implementing security? This inefficiency is exactly where UTMStack intervenes.
Turning Logs Into Living Evidence
At its core, UTMStack transforms raw data into regulatory proof. Because it centralizes logs from across the entire organizational ecosystem, it can dynamically assess whether controls are functioning as intended.
The platform doesn’t just store data; it interrogates it. Consider these three critical pillars of automation:
1. Encryption Enforcement
UTMStack monitors logs for mandatory encryption, whether data is at rest or in transit. If a TLS connection fails due to an untrusted certificate authority, the system doesn’t just log the error—it flags a control failure instantly.
2. Two-Factor Authentication (2FA) Validation
By aggregating authentication logs—such as those from Office365—UTMStack verifies that MFA requirements are satisfied. If a user bypasses a required push notification, the system generates an immediate alert for remediation.
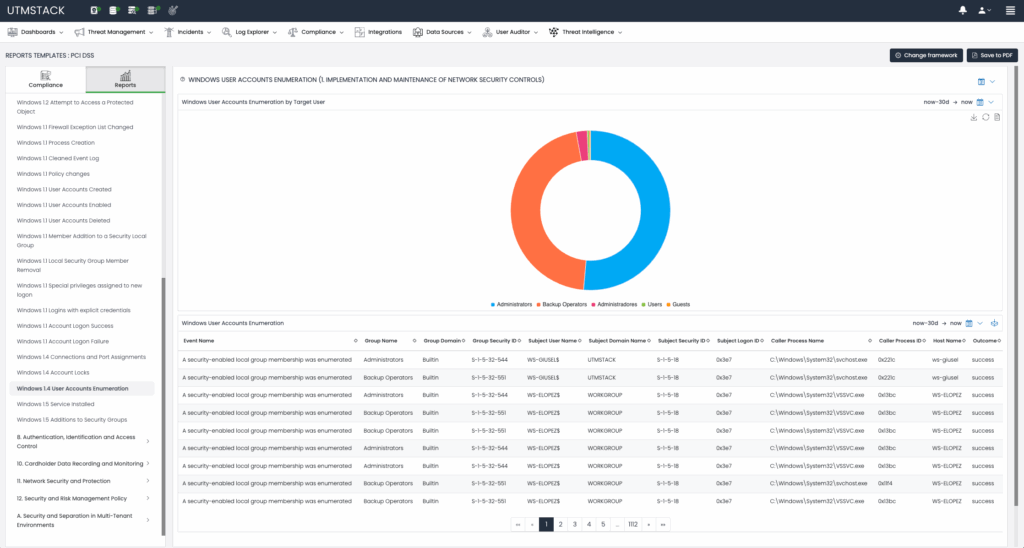
3. Continuous User Activity Auditing
Privileged account usage and anomalous data access patterns are monitored natively. Once integrations are configured, the platform automatically checks for compliance risks without requiring manual queries.
Empowering the Non-Coder: The No-Code Builder
Perhaps the most disruptive element of UTMStack is its no-code compliance automation builder. Historically, custom compliance logic required a developer; now, it requires a vision.
Compliance officers can now visually define control logic, establish real-time monitoring conditions, and schedule tailored reports. This agility allows teams to pivot as quickly as regulators change their minds.
Solving the CMMC Puzzle
For those navigating the Cybersecurity Maturity Model Certification (CMMC), the requirements for data confidentiality and processing integrity are daunting. UTMStack simplifies this by mapping continuous log data—from firewall configs to audit trails—directly to CMMC control numbers.
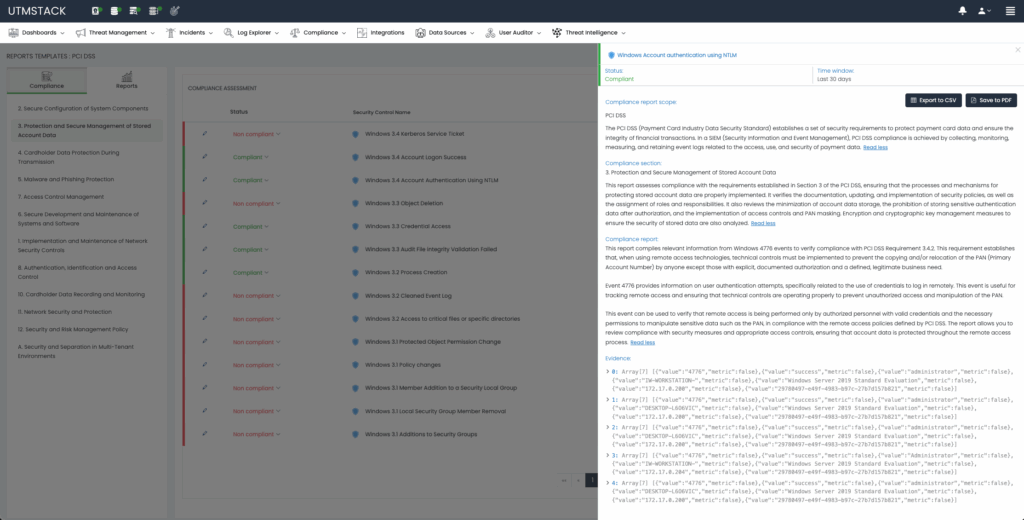
When a control is flagged as non-compliant, the platform doesn’t leave the analyst guessing. Using Retrieval-Augmented Generation (RAG), an AI-driven technique, UTMStack provides specific remediation steps to bridge the gap.
Does the prospect of a “permanent audit” feel overwhelming, or does it feel like the only way to ensure true security?
The API-First Ecosystem
UTMStack is designed to play well with others. Its API-first approach means that compliance data can flow seamlessly into existing Governance, Risk, and Compliance (GRC) platforms.
This “single pane of glass” allows organizations to combine automated technical checks with manual declarations, creating a comprehensive audit trail that is virtually bulletproof.
The Future of Governance: Why Automation is Non-Negotiable
The shift toward compliance automation represents a broader evolution in cybersecurity. We are moving away from “point-in-time” security—where a company is secure on the day of the audit—toward “continuous security.”
By integrating SIEM and XDR capabilities, UTMStack ensures that the data used for compliance is the same data used for threat detection. This convergence eliminates the silo between the security operations center (SOC) and the compliance office.
As we look toward a future of increasing regulatory scrutiny, tools that leverage NIST guidelines and open-source flexibility will be the ones that survive. Automation isn’t just about efficiency; it’s about survival in a landscape where a single missed log can lead to a million-dollar fine.
Frequently Asked Questions About Compliance Automation
- What is compliance automation in cybersecurity?
- Compliance automation is the use of software tools to continuously monitor security controls and automatically gather evidence for regulatory frameworks like GDPR, HIPAA, and CMMC, replacing manual spreadsheets.
- How does UTMStack facilitate automated compliance management?
- UTMStack uses an open-source SIEM and XDR approach to centralize logs and apply automated correlation rules that dynamically evaluate whether specific security controls are being met in real-time.
- Can compliance automation help with CMMC requirements?
- Yes, UTMStack specifically automates CMMC controls by analyzing firewall configurations and user access patterns to provide detailed reports on specific control numbers and levels.
- Does compliance automation require advanced programming skills?
- Not with UTMStack; it features a no-code compliance automation builder that allows teams to visually define control logic and schedule reports via a drag-and-drop interface.
- How does AI enhance automated compliance evidence?
- UTMStack employs Retrieval-Augmented Generation (RAG) to analyze non-compliance events and provide security engineers with precise, AI-driven remediation steps.
Disclaimer: This article provides technical information regarding regulatory compliance tools and does not constitute legal advice. Organizations should consult with certified compliance auditors to ensure full adherence to specific legal frameworks.
The original insights on this topic were first explored in the piece Automating Compliance Management with UTMStack’s Open Source SIEM & XDR via Linux.com.
Join the movement toward transparent, automated security. We invite the cybersecurity community to help shape the future of this tool. Explore the codebase and contribute via GitHub Discussions, or collaborate in real-time through the Discord Channel.
What is the biggest bottleneck in your current audit process? Share your experience in the comments below and share this article with your team to start the conversation!
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.

