Cloudflare Outage Exposes Website Security Gaps, Prompts Urgent Self-Assessment
A widespread, intermittent outage at Cloudflare on Tuesday disrupted access to numerous popular websites, forcing some organizations to temporarily bypass the platform to maintain service. While restoring connectivity was the immediate priority, security experts warn this unplanned shift may have inadvertently triggered a significant security assessment – revealing vulnerabilities many companies didn’t know they had.
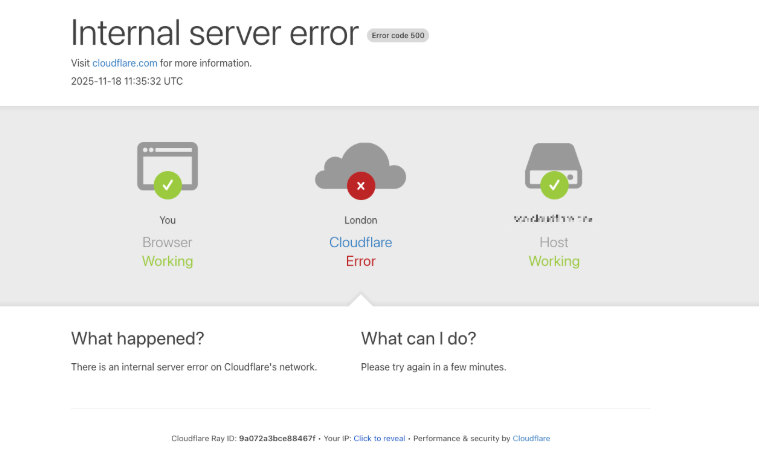
The disruption, first acknowledged by Cloudflare around 6:30 EST/11:30 UTC on November 18th, involved fluctuating service availability. Many websites relying on Cloudflare found themselves unable to quickly switch away due to inaccessibility of the Cloudflare portal and, in some cases, dependence on Cloudflare for Domain Name System (DNS) services. However, those who could temporarily reroute traffic are now facing a critical security review.
The Hidden Security Risks of Cloudflare Dependence
Aaron Turner, a faculty member at IANS Research, explains that Cloudflare’s Web Application Firewall (WAF) effectively blocks a substantial portion of malicious traffic, including attacks listed in the OWASP Top Ten – such as credential stuffing, cross-site scripting (XSS), and SQL injection. The outage, however, highlighted a potential over-reliance on this protection.
“Organizations may have become complacent, allowing gaps in their own application security because Cloudflare was handling the heavy lifting,” Turner stated. “Developers might have overlooked robust SQL injection defenses, assuming Cloudflare would catch it. Security QA processes may have been less rigorous, relying on Cloudflare as a compensating control.”
One company Turner is working with experienced a dramatic surge in log volume during the outage, struggling to differentiate between legitimate traffic and malicious attempts. This underscores the challenge of identifying and mitigating threats without the continuous protection of a WAF like Cloudflare’s.
The window of vulnerability, estimated at approximately eight hours, presented a prime opportunity for cybercriminals. As Turner points out, attackers actively monitoring targets would have immediately recognized the removal of Cloudflare’s defenses and launched new attacks accordingly. What if an attacker had been attempting to breach a system, only to find the protective layer suddenly removed?
A “Free” Tabletop Exercise in Cybersecurity
Nicole Scott, senior product marketing manager at Replica Cyber, aptly described the outage as “a free tabletop exercise.” She emphasized the importance of analyzing internal responses to the disruption, noting how organizations circumvented standard procedures and whether “shadow IT” solutions emerged under pressure.
Scott recommends organizations ask themselves critical questions:
- What security measures (WAF, bot protection, geo-blocking) were disabled or bypassed, and for how long?
- What emergency DNS or routing changes were implemented, and who authorized them?
- Did employees resort to personal devices, home networks, or unapproved SaaS applications to maintain access?
- Were any temporary services, tunnels, or vendor accounts created as quick fixes?
- Are these temporary changes being reversed, or have they become permanent workarounds?
- What is the pre-defined fallback plan for future incidents, avoiding ad-hoc improvisation?
The incident serves as a stark reminder that relying on a single provider, even a robust one like Cloudflare, creates a single point of failure. Martin Greenfield, CEO at Quod Orbis, advises organizations to “split their estate” – diversifying WAF and DDoS protection, utilizing multi-vendor DNS, and segmenting applications to prevent cascading outages.
Did You Know? Cloudflare estimates that roughly 20% of all websites utilize its services, demonstrating the significant concentration of internet infrastructure within a handful of cloud providers.
Root Cause and Future Mitigation
In a postmortem published Tuesday evening, Cloudflare CEO Matthew Prince attributed the outage to a database permissions issue that caused an unexpected expansion of a “feature file” used by its Bot Management system. This oversized file was then propagated across the entire network, leading to the service disruption. Read the full postmortem here.
The incident highlights the inherent risks of complex, interconnected systems and the importance of robust monitoring and automated safeguards. But what steps can organizations take *now* to better prepare for similar disruptions in the future?
Frequently Asked Questions About the Cloudflare Outage
What is a Web Application Firewall (WAF) and why is it important?
A WAF is a security mechanism that filters, monitors, and blocks malicious HTTP traffic traveling to a web application, protecting against common attacks like SQL injection and cross-site scripting.
How does the Cloudflare outage relate to the OWASP Top Ten?
The OWASP Top Ten lists the most critical web application security risks. Cloudflare’s WAF is designed to mitigate many of these risks, and the outage exposed organizations to potential vulnerabilities in these areas.
What is “shadow IT” and why is it a concern during outages?
“Shadow IT” refers to IT systems and solutions built and used inside an organization without explicit IT department approval. During outages, employees may turn to these unapproved tools, creating security risks.
What does it mean to “split your estate” in terms of cybersecurity?
“Splitting your estate” means diversifying your security infrastructure by using multiple vendors for services like WAF, DDoS protection, and DNS, reducing reliance on a single point of failure.
How can organizations improve their incident response planning for cloud provider outages?
Organizations should develop a pre-defined fallback plan for cloud provider outages, including clear procedures for DNS rerouting, WAF activation, and communication protocols.
What is a postmortem and why are they important?
A postmortem is a detailed analysis of an incident, like the Cloudflare outage, to identify root causes, contributing factors, and lessons learned for future prevention.
This incident serves as a critical wake-up call for organizations of all sizes. Proactive security measures, diversified infrastructure, and robust incident response planning are no longer optional – they are essential for maintaining a secure and resilient online presence.
Share this article with your network to raise awareness about the importance of proactive cybersecurity! What steps is your organization taking to mitigate the risks of cloud provider outages? Share your thoughts in the comments below.
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.