Understanding Encryption: A Comprehensive Glossary
The digital landscape is increasingly reliant on secure communication, making encryption a cornerstone of modern technology. But what exactly *is* encryption? And what are the key terms you need to know to navigate this complex field? This glossary breaks down the essential vocabulary, providing clarity on this vital security infrastructure.
The Foundation of Secure Data Transmission
Encryption is the process of converting information or data into a code, especially to prevent unauthorized access. It’s a fundamental practice in protecting sensitive data, from online banking transactions to personal communications. Without encryption, our digital lives would be significantly more vulnerable to cyber threats.
Hash Functions: The Digital Fingerprint
A hash function is a one-way cryptographic function that takes an input (or ‘message’) and produces a fixed-size output, known as a hash value or digest. This digest acts as a unique ‘fingerprint’ of the data. Even a minor change to the input data will result in a drastically different hash value. Hash functions are crucial for verifying data integrity.
SSL/TLS: Securing Connections
Secure Sockets Layer (SSL) and its successor, Transport Layer Security (TLS), are cryptographic protocols that provide communication security over a computer network. You’ll recognize SSL/TLS through the “https” prefix in web addresses and the padlock icon in your browser. These protocols encrypt the data exchanged between your browser and the website server, protecting it from eavesdropping and tampering.
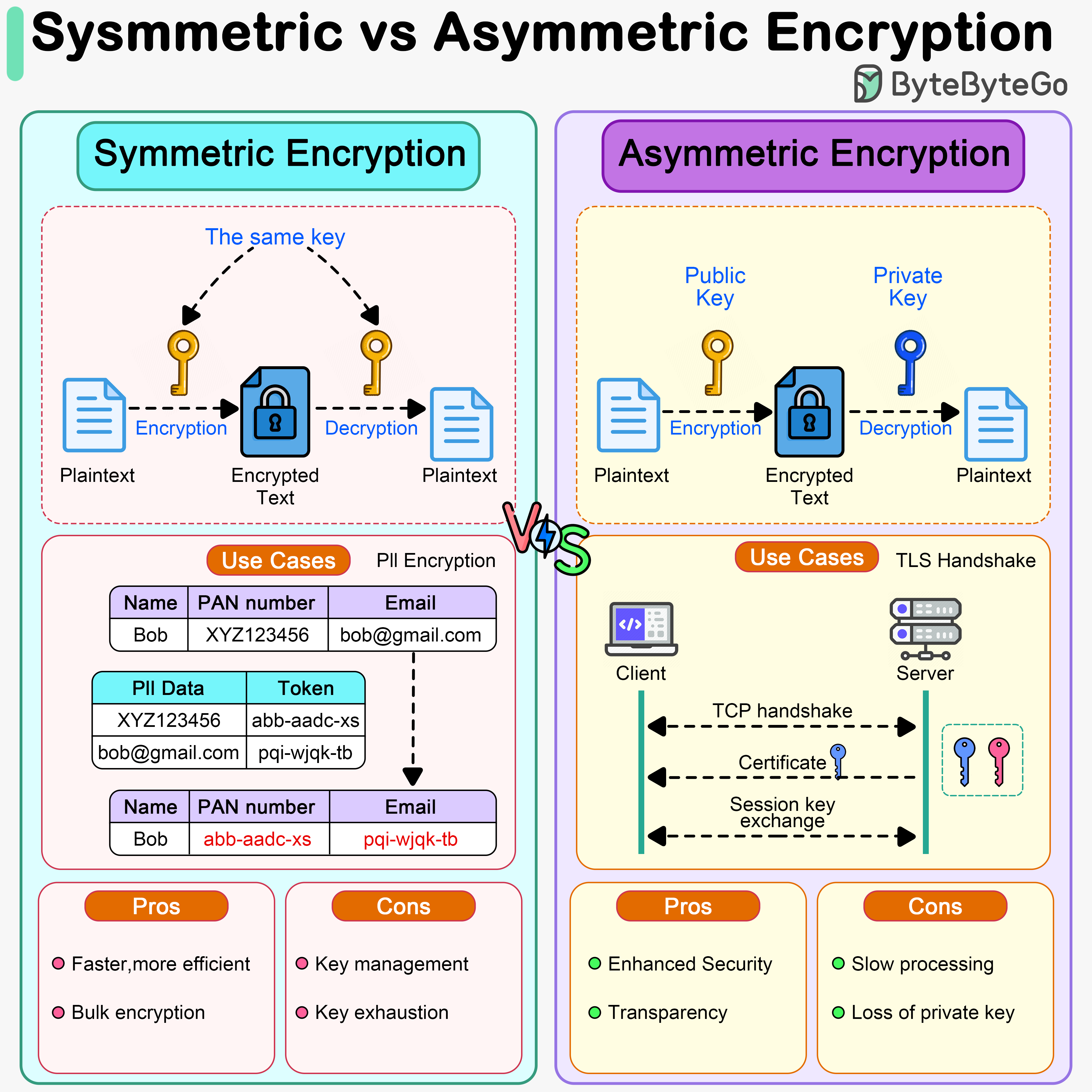
Symmetric vs. Asymmetric Encryption
Encryption methods fall into two primary categories: symmetric and asymmetric. Symmetric encryption uses the same key for both encryption and decryption, making it faster but requiring a secure method for key exchange. Asymmetric encryption, also known as public-key cryptography, uses a pair of keys – a public key for encryption and a private key for decryption. This eliminates the need for secure key exchange but is computationally more intensive.
Advanced Encryption Standard (AES)
AES is a widely used symmetric-key encryption algorithm adopted by the U.S. government as a standard. It’s known for its strong security and efficiency, making it a popular choice for securing a wide range of applications and data.
Data Encryption at Rest vs. Data in Transit
Data encryption isn’t a one-size-fits-all solution. It’s crucial to protect data both when it’s stored (at rest) and when it’s being transmitted (in transit). Encrypting data at rest safeguards it from unauthorized access if a storage device is compromised. Encrypting data in transit protects it from interception during transmission.
Considering the increasing sophistication of cyberattacks, are current encryption standards sufficient to protect our data in the long term? What role will quantum computing play in the future of encryption?
Further resources on encryption can be found at The National Institute of Standards and Technology (NIST) and The Electronic Frontier Foundation (EFF).
Frequently Asked Questions About Encryption
Here are some common questions about encryption:
- What is the primary purpose of encryption?
Encryption’s main goal is to protect the confidentiality and integrity of data by converting it into an unreadable format, preventing unauthorized access. - Is encryption always foolproof?
While encryption is a powerful security tool, it’s not foolproof. The strength of encryption depends on the algorithm used, the key length, and the implementation. - What is the difference between encryption and hashing?
Encryption is a two-way process (encryption and decryption), while hashing is a one-way process (creating a digest). - How does SSL/TLS encryption work?
SSL/TLS uses a combination of symmetric and asymmetric encryption to establish a secure connection between a client and a server. - Can encryption protect against all cyber threats?
Encryption is a crucial layer of security, but it doesn’t protect against all threats, such as phishing attacks or malware.
Stay informed about the latest developments in cybersecurity and encryption to protect yourself and your data in an increasingly interconnected world.
Share this article with your network to help spread awareness about the importance of encryption! What other encryption terms do you find confusing? Let us know in the comments below.
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.