A staggering 82% of US security breaches now originate from insider threats, a figure that’s quietly doubled in the last decade. The recent case involving Ashley Tellis, a prominent Indian-American defense strategist, isn’t an isolated incident; it’s a symptom of a far more pervasive and dangerous trend: the increasing vulnerability of national security apparatus to subtle, yet potent, forms of influence. The allegations against Tellis – possessing classified documents and maintaining undisclosed contacts with Chinese officials – have sent ripples through Washington, but the true story lies not just in the specifics of this case, but in what it reveals about the evolving landscape of geopolitical intelligence gathering.
The Shifting Sands of Influence Operations
For decades, espionage conjured images of cloak-and-dagger operations and dramatic defectors. Today, the battlefield is far more nuanced. The Tellis case, as reported by the BBC, NDTV, and the India Today, suggests a pattern of engagement that doesn’t fit neatly into traditional espionage paradigms. Instead, it points to a sophisticated effort to cultivate relationships and potentially gain access to sensitive information through seemingly legitimate channels – dinners, gift exchanges, and professional consultations. This represents a shift from overt intelligence gathering to a more insidious form of influence peddling.
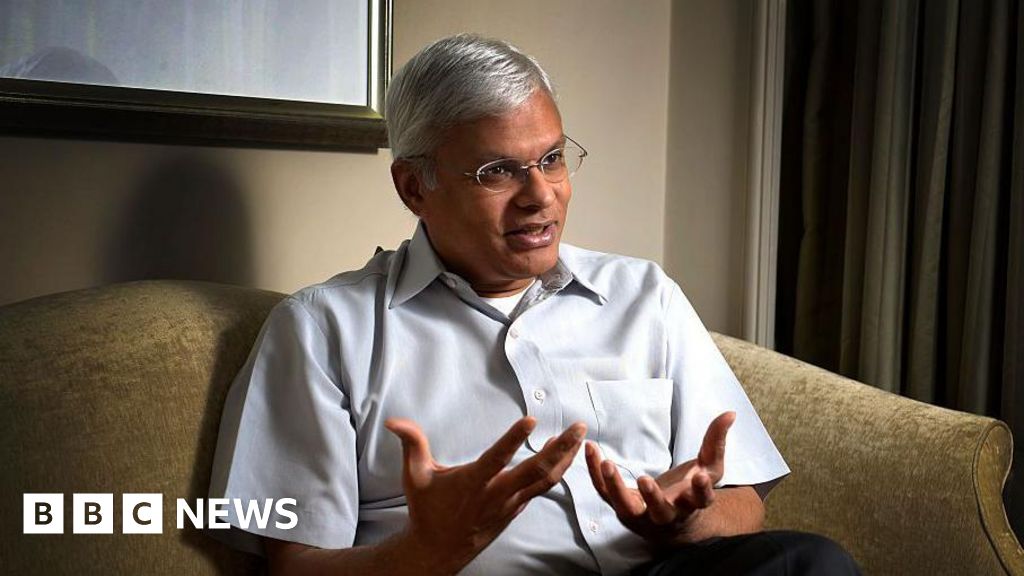
The fact that Tellis, a highly respected figure with deep ties to the US defense establishment, allegedly engaged in these activities underscores the challenge. It’s no longer enough to simply vet individuals at the point of entry; continuous monitoring and a rigorous understanding of potential conflicts of interest are paramount. The Times of India’s reporting on Tellis’s background, tracing his journey from St. Xavier’s College to a position of influence in US strategic circles, highlights the importance of understanding the entire lifecycle of an individual’s career and potential vulnerabilities.
The Rise of the ‘Strategic Consultant’
A key element of this evolving threat landscape is the proliferation of former government officials transitioning into lucrative roles as strategic consultants. While perfectly legal, this creates inherent risks. These individuals possess invaluable knowledge and networks, making them attractive targets for foreign governments and corporations seeking to gain an edge. The line between providing legitimate advice and inadvertently – or intentionally – sharing sensitive information can become dangerously blurred. This is where the FBI’s investigation, detailed in India Today’s coverage of the “Ashley Tellis Files,” becomes particularly concerning. The focus on seemingly innocuous items like a Manila envelope and gift bags suggests a deliberate attempt to establish a pattern of reciprocal favors, potentially creating leverage.
The China Factor: A New Cold War Dynamic?
The alleged involvement of Chinese officials in the Tellis case adds another layer of complexity. China has demonstrably increased its intelligence gathering efforts in recent years, employing a wide range of tactics, from cyber espionage to economic coercion. The focus on individuals with access to US defense policy aligns with China’s strategic objectives of challenging US dominance and expanding its global influence. This isn’t simply about stealing secrets; it’s about understanding US thinking, anticipating future moves, and ultimately, shaping the geopolitical landscape to China’s advantage.
The implications extend beyond the immediate case. It raises questions about the effectiveness of current vetting procedures, the adequacy of counterintelligence measures, and the potential for similar vulnerabilities within other government agencies and private sector firms. The US needs to adopt a more proactive and comprehensive approach to protecting its national security interests, one that recognizes the evolving nature of the threat and the importance of building resilience against foreign influence.
Counterintelligence efforts must evolve beyond traditional methods, incorporating advanced data analytics, behavioral analysis, and a greater emphasis on identifying and mitigating insider risks. Furthermore, stricter regulations governing the post-government employment of former officials may be necessary to prevent conflicts of interest and protect sensitive information.
| Threat Vector | Traditional Approach | Evolving Approach |
|---|---|---|
| Espionage | Identifying and neutralizing foreign agents | Detecting and mitigating subtle influence operations |
| Insider Threat | Background checks and security clearances | Continuous monitoring and behavioral analysis |
| Foreign Influence | Diplomatic pressure and sanctions | Strengthening resilience and protecting critical infrastructure |
Looking Ahead: The Future of Geopolitical Intelligence
The Ashley Tellis case serves as a stark warning. The era of traditional espionage is giving way to a new age of subtle influence, where the lines between public service, private enterprise, and foreign interests are increasingly blurred. The US – and indeed, all nations – must adapt to this new reality by investing in advanced counterintelligence capabilities, strengthening ethical guidelines for former government officials, and fostering a culture of vigilance and transparency. The stakes are simply too high to ignore.
Frequently Asked Questions About Geopolitical Intelligence
What are the biggest challenges facing US counterintelligence today?
The biggest challenges include the increasing sophistication of foreign influence operations, the proliferation of dual-use technologies, and the difficulty of detecting subtle insider threats.
How can individuals protect themselves from foreign influence?
Be aware of potential attempts to cultivate relationships or solicit information. Report any suspicious activity to the appropriate authorities. Practice good cybersecurity hygiene.
What role does technology play in the future of intelligence gathering?
Technology will play an increasingly important role, enabling more sophisticated data analysis, predictive modeling, and automated threat detection. However, it also creates new vulnerabilities that must be addressed.
What are your predictions for the future of geopolitical intelligence and the evolving threat landscape? Share your insights in the comments below!
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.