Kimwolf Botnet Disrupts Anonymous Network I2P in Attempt to Evade Takedown
A massive Internet of Things (IoT) botnet known as Kimwolf has launched a disruptive campaign against The Invisible Internet Project (I2P), a decentralized and encrypted network designed to provide anonymous online communication. The attacks began as Kimwolf’s operators sought to leverage I2P to shield their command and control servers from disruption, inadvertently crippling the privacy network in the process.
Kimwolf, which emerged in late 2025, has rapidly infected millions of vulnerable devices – including streaming media players, digital photo frames, and routers – transforming them into relays for malicious traffic and enabling abnormally large distributed denial-of-service (DDoS) attacks. Recent reports detail the botnet’s significant impact on internet infrastructure.
Understanding I2P: A Deep Dive into Anonymous Networking
I2P is fundamentally different from the conventional internet. It’s a darknet, meaning it’s a network built on top of the internet but hidden from standard detection methods. Instead of relying on centralized servers, I2P operates as a peer-to-peer network, routing data through multiple layers of encryption across volunteer-operated nodes. This process obscures both the sender and receiver’s locations, creating a secure and censorship-resistant environment. As the I2P website explains, the network is designed for private websites, secure messaging, and confidential data sharing.
The strength of I2P lies in its decentralized nature. Unlike traditional networks with single points of failure, I2P’s distributed architecture makes it incredibly resilient to attacks. However, as the recent Kimwolf incident demonstrates, even robust systems are vulnerable to novel and unexpected threats. The network’s reliance on volunteer-operated nodes also means its capacity is limited and susceptible to being overwhelmed.
The concept of anonymity networks like I2P is rooted in the desire for privacy and freedom of expression. They provide a haven for journalists, activists, and individuals seeking to communicate without fear of surveillance or censorship. However, this same anonymity can also be exploited by malicious actors, presenting a constant challenge for network administrators and security researchers.
Kimwolf’s Assault on I2P: A Sybil Attack
On February 3rd, I2P users began reporting widespread disruptions. Complaints flooded the organization’s GitHub page, detailing tens of thousands of new routers suddenly joining the network, overwhelming existing infrastructure and preventing legitimate users from connecting. Users observed a rapid influx of systems unable to transmit data, effectively paralyzing the network. One user reported their router freezing when connection attempts exceeded 60,000.
I2P users complaining about service disruptions from a rapidly increasing number of routers suddenly swamping the network.
The cause of the disruption quickly became apparent. Kimwolf’s operators openly admitted, in their Discord channel, to attempting to integrate 700,000 infected bots as nodes on the I2P network. This action constituted a Sybil attack – a malicious tactic where a single entity creates numerous fake identities to disrupt a peer-to-peer system.
The Kimwolf botmaster openly discusses what they are doing with the botnet in a Discord channel.
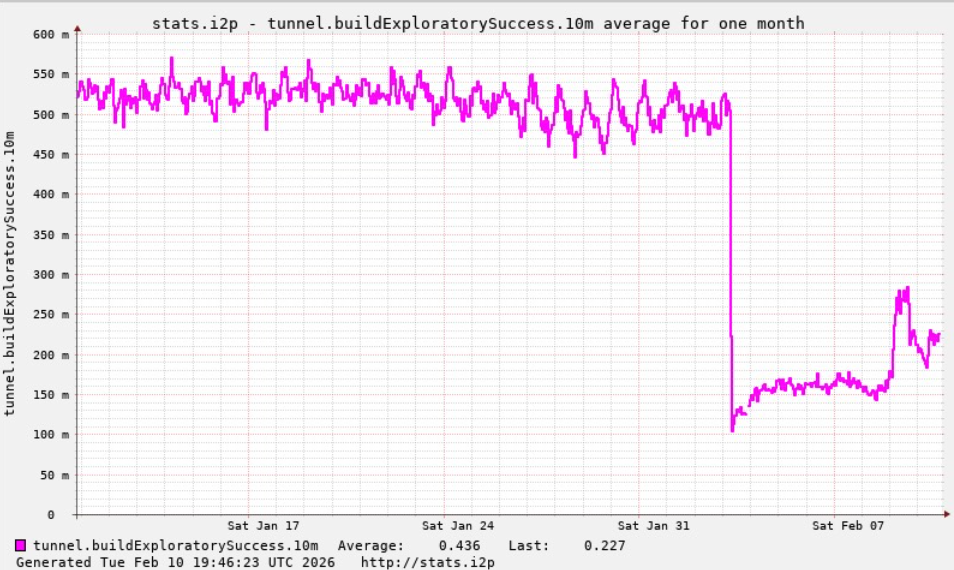
A graph shared by I2P developers showing a marked drop in successful connections on the I2P network around the time the Kimwolf botnet started trying to use the network for fallback communications.
The scale of the attack was significant. While I2P’s Wikipedia page previously estimated the network at around 55,000 computers, Lance James, founder of Unit 221B and the original founder of I2P, revealed the current network size is closer to 15,000-20,000 devices. The attempted influx of Kimwolf bots far exceeded the network’s capacity.
Kimwolf’s Strategic Shift and Potential Weaknesses
According to Benjamin Brundage, founder of Synthient, the Kimwolf operators are attempting to establish a command and control network resilient to takedown efforts. They’ve been experimenting with both I2P and Tor as potential backup systems. “I don’t think their goal is to take I2P down,” Brundage stated, “It’s more they’re looking for an alternative to keep the botnet stable in the face of takedown attempts.”
Interestingly, recent developments suggest Kimwolf may be facing internal challenges. Brundage reports that the botnet’s operators have alienated key developers and operators, leading to a significant error that resulted in a loss of over 600,000 infected systems. “It seems like they’re just testing stuff, like running experiments in production,” Brundage observed. “But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing.”
Do you think the Kimwolf botnet’s reliance on vulnerable IoT devices highlights a systemic security flaw in the Internet of Things? And what measures can individuals take to protect their devices from becoming part of a botnet?
The Kimwolf botnet previously caused disruptions for Cloudflare last year by directing millions of infected devices to use its DNS settings, temporarily displacing major websites like Amazon, Apple, Google, and Microsoft in Cloudflare’s rankings. More details on this incident can be found here.
I2P is currently operating at roughly half its normal capacity, but a new release is underway that aims to improve stability for users. The network’s resilience will be crucial in the face of ongoing threats.
Frequently Asked Questions About the Kimwolf Botnet and I2P
A: Kimwolf is a large network of compromised Internet of Things (IoT) devices used to launch distributed denial-of-service (DDoS) attacks and other malicious activities.
A: Kimwolf attempted to use I2P as a backup command and control network, overwhelming the system with a massive influx of bots and disrupting service for legitimate users.
A: A Sybil attack involves a single entity creating numerous fake identities to gain control or disrupt a network. Kimwolf’s attempt to flood I2P with bots is a classic example of this type of attack.
A: While the attack caused significant disruption, I2P remains a secure network. Developers are working on improvements to enhance its resilience against future attacks.
A: Regularly update your devices’ firmware, use strong and unique passwords, and disable unnecessary features to minimize your risk of infection.
A: Kimwolf’s operators have also experimented with using Tor as a backup command and control network, but there have been no recent reports of widespread disruptions to Tor.
Share this article to help raise awareness about the evolving threats to online privacy and security. Join the conversation in the comments below – what are your thoughts on the future of anonymous networks in the face of increasingly sophisticated botnets?
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.

