The Growing Threat of ‘Parked’ Domains: Scams and Malware Lurk for Unwary Internet Users
A new study reveals a dramatic surge in malicious activity originating from parked domains – expired or misspelled web addresses – with over 90% now redirecting visitors to scams, malware, and other harmful content. What was once a minor risk has become a significant threat to online security.
The Evolution of a Digital Danger
For years, when a domain name lapsed or was intentionally left unused, it often ended up in a “parking” state. Domain parking companies would display advertisements, generating revenue from accidental visitors. While not entirely benign, the risk was relatively low. In 2014, research indicated that less than 5% of visits to parked domains resulted in redirection to malicious sites (USENIX Security 2014 Paper). Today, that landscape has drastically changed.
Infoblox Research Exposes the Scale of the Problem
Recent experiments conducted by the security firm Infoblox paint a disturbing picture. Over 90% of visitors to parked domains are now directed to illegal content, scams promising fake antivirus software, scareware, or outright malware. This shift is driven by a complex resale chain, where parking companies sell traffic to advertisers who, in turn, may resell it to malicious actors.
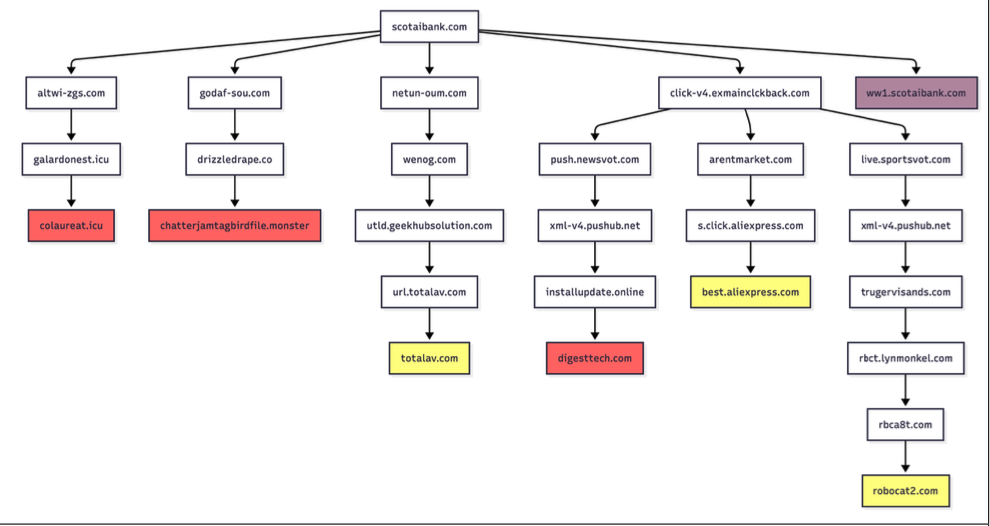
The vulnerability isn’t uniform. Infoblox discovered that using a Virtual Private Network (VPN) or a non-residential internet address can bypass the malicious redirects. For example, a Scotiabank customer accidentally typing “scotaibank[.]com” will likely reach a standard parking page while using a VPN, but a user with a residential IP address faces immediate redirection to a scam site. This highlights the profiling tactics employed by these malicious networks.
Typosquatting and the Rise of Sophisticated Attacks
The problem extends beyond simple misspellings. Threat actors are actively registering lookalike domains – “typosquatting” – targeting popular websites. One individual controls nearly 3,000 such domains, including “gmai[.]com,” which is actively receiving and processing email intended for Gmail users. This domain has also been linked to business email compromise (BEC) campaigns, distributing malware via fraudulent payment notifications.
Infoblox identified a network of typosquatting domains targeting major internet destinations like Craigslist, YouTube, Google, Wikipedia, Netflix, TripAdvisor, Yahoo, eBay, and Microsoft. A list of these domains (with dots replaced by commas) is available for review.
How Attackers Profile and Target Victims
According to David Brunsdon, a threat researcher at Infoblox, the redirection process isn’t immediate. Parked pages gather information about visitors – IP geolocation, device fingerprinting, and cookies – to determine the most effective malicious destination. “It was often a chain of redirects – one or two domains outside the parking company – before the threat arrives,” Brunsdon explained. “Each time, the device is profiled again and again.”
Interestingly, some attackers are employing more nuanced tactics. The domain “domaincntrol[.]com” redirects visitors using Cloudflare’s DNS resolvers (1.1.1.1) to malicious sites, while others are simply refused access. This suggests a targeted approach, potentially based on DNS provider usage.
Even government domains aren’t immune. A researcher accidentally visiting “ic3[.]org” instead of “ic3[.]gov” – the FBI’s Internet Crime Complaint Center – was redirected to a fake “Drive Subscription Expired” page, demonstrating the widespread nature of this threat.
While the Infoblox report doesn’t directly implicate domain parking or advertising platforms, it highlights a breakdown in the traffic resale chain, where the final advertiser often has no direct relationship with the parking company.
Recent changes to Google Adsense policies, requiring advertisers to actively opt-in to displaying ads on parked domains, may inadvertently exacerbate the problem by further concentrating traffic in the hands of malicious actors.
What steps can individuals take to protect themselves from these evolving threats? Are current security measures sufficient to combat this growing problem?
Frequently Asked Questions About Parked Domain Threats
What are parked domains and why are they dangerous?
Parked domains are expired or unused web addresses that are often filled with advertisements. They’ve become dangerous because malicious actors are increasingly using them to redirect visitors to scam and malware sites.
How can I avoid being redirected to malicious sites from parked domains?
Using a VPN or a non-residential internet address can help bypass malicious redirects. Always double-check the URL before entering sensitive information.
What is typosquatting and how does it relate to this threat?
Typosquatting is the practice of registering domain names that are slight misspellings of popular websites. Attackers use these domains to trick users into visiting malicious sites.
Are all domain parking services malicious?
No, not all domain parking services are malicious. However, the resale of traffic through multiple intermediaries creates opportunities for malicious actors to exploit the system.
What role does Google Adsense play in this issue?
Recent changes to Google Adsense policies, requiring advertisers to opt-in to displaying ads on parked domains, may inadvertently concentrate traffic in the hands of malicious actors.
How can I protect myself from email scams related to parked domains?
Carefully verify the sender’s email address and avoid clicking on links or downloading attachments from suspicious emails. Be especially cautious if an email asks for personal or financial information.
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.

