Alleged Jabber Zeus Developer ‘MrICQ’ Extradited to U.S., Faces Decades in Prison
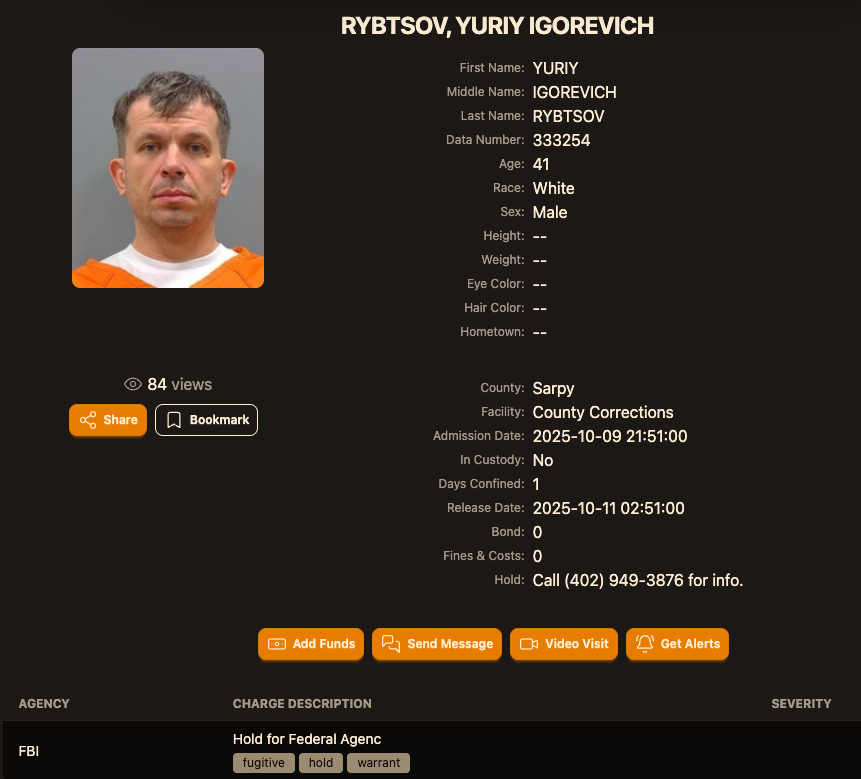
After more than a decade evading justice, Yuriy Igorevich Rybtsov, a 41-year-old Ukrainian national accused of being a core developer for the devastating Jabber Zeus cybercrime organization, is now in U.S. custody. Rybtsov, previously known only by his online alias “MrICQ” in federal indictments, was recently extradited from Italy, where he had been fighting legal battles to avoid facing charges in the United States.
The arrest marks a significant victory for law enforcement agencies that have long pursued the remnants of Jabber Zeus, a group responsible for stealing tens of millions of dollars from businesses worldwide through sophisticated banking malware and intricate money laundering schemes. But what made Jabber Zeus so uniquely dangerous, and what does Rybtsov’s capture mean for the broader landscape of cybercrime?
The Rise and Fall of Jabber Zeus
Jabber Zeus gained notoriety in the early 2010s for its innovative use of the Zeus banking trojan, a malicious program designed to steal login credentials and financial data. Unlike earlier iterations of Zeus, the Jabber Zeus crew customized the malware to send real-time alerts via the Jabber instant messaging platform whenever a victim entered a one-time passcode at a financial institution. This allowed the hackers to intercept authentication codes, bypassing even multi-factor authentication systems.
The group primarily targeted small to mid-sized businesses, employing a “man-in-the-browser” attack technique that silently intercepted data submitted through web forms. Once inside a company’s accounts, they would manipulate payroll systems to add fraudulent “money mules” – individuals recruited through deceptive work-at-home schemes – who would then funnel stolen funds through a network of wire transfers to accounts in Ukraine and the United Kingdom.
According to a 2012 indictment filed in Nebraska, Rybtsov, operating as “John Doe #3,” played a crucial role in handling notifications of compromised victims and facilitating the laundering of illicit proceeds. His arrest represents a key piece falling into place in a complex, years-long investigation.
Image: lockedup dot wtf
The Jabber Zeus operation wasn’t conducted in a vacuum. Investigators discovered the group collaborated directly with Evgeniy Mikhailovich Bogachev, the alleged author of the original Zeus Trojan, who remains on the FBI’s “Most Wanted” list with a $3 million reward for information leading to his arrest. The FBI continues to seek information on Bogachev.
However, Rybtsov wasn’t the sole leader. Authorities believe the true mastermind behind Jabber Zeus was Maksim Yakubets, a 38-year-old Ukrainian with Russian citizenship known online as “Aqua.” Yakubets would later evolve into the leader of “Evil Corp,” an even more sophisticated cybercrime ring responsible for over $100 million in losses through the Dridex (a.k.a. Bugat) trojan. More details on Evil Corp can be found in this 2019 report.

Vyacheslav “Tank” Penchukov, seen here performing as “DJ Slava Rich” in Ukraine, in an undated photo from social media.
Vyacheslav “Tank” Penchukov, a key associate of Yakubets, was arrested in Switzerland in 2022 and sentenced to 18 years in prison last year, ordered to pay over $73 million in restitution. Read more about Penchukov’s sentencing here.
The investigation into Jabber Zeus was significantly aided by Lawrence Baldwin, founder of myNetWatchman, a threat intelligence company that gained access to the group’s Jabber chat server in 2009. Baldwin’s real-time monitoring of the hackers’ communications provided invaluable intelligence to law enforcement and allowed for the timely warning of potential victims.
Baldwin’s insights revealed the sophistication of the Jabber Zeus crew, including their development of a custom “backconnect” component that allowed them to relay bank account takeovers through the victim’s own infected PC, making it appear as if the transactions originated from a legitimate source. This level of technical prowess made Jabber Zeus a particularly formidable threat.
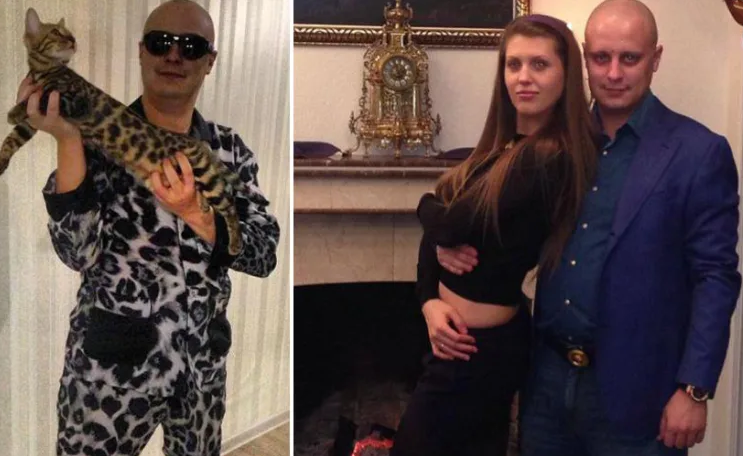
Evgeniy M. Bogachev, in undated photos.
What steps can businesses take to protect themselves from similar attacks? Investing in robust cybersecurity measures, including endpoint detection and response (EDR) systems, employee training on phishing awareness, and regular security audits, are crucial. Do you believe current cybersecurity protocols are sufficient to combat these evolving threats?
Frequently Asked Questions About Jabber Zeus
What was the primary goal of the Jabber Zeus cybercrime group?
The primary goal of the Jabber Zeus group was to steal financial data, particularly banking login credentials, from businesses and individuals to facilitate fraudulent money transfers.
How did the Jabber Zeus malware bypass multi-factor authentication?
Jabber Zeus utilized a component called “Leprechaun” that intercepted one-time passcodes entered by victims, effectively bypassing multi-factor authentication systems.
Who is Evgeniy Bogachev and what was his role in the Jabber Zeus operation?
Evgeniy Bogachev is the alleged author of the original Zeus Trojan and collaborated with the Jabber Zeus crew to customize and enhance the malware.
What is the current status of Maksim Yakubets, the alleged leader of Jabber Zeus and Evil Corp?
Maksim Yakubets remains at large and is currently on the FBI’s Most Wanted list with a $5 million reward for information leading to his arrest.
How can businesses protect themselves from attacks similar to those carried out by Jabber Zeus?
Businesses can protect themselves by implementing robust cybersecurity measures, including endpoint detection and response systems, employee training, and regular security audits.
What role did Lawrence Baldwin and myNetWatchman play in disrupting the Jabber Zeus operation?
Lawrence Baldwin and myNetWatchman gained access to the Jabber Zeus group’s chat server, providing invaluable intelligence to law enforcement and enabling the warning of potential victims.
Rybtsov’s extradition and impending trial represent a significant step towards holding the perpetrators of these crimes accountable. The case serves as a stark reminder of the ever-present threat posed by cybercriminals and the importance of international cooperation in combating online fraud.
Share this article to raise awareness about the dangers of cybercrime and the ongoing efforts to bring these criminals to justice. What further steps do you think governments and businesses should take to enhance cybersecurity and protect against these evolving threats? Join the conversation in the comments below.
Disclaimer: This article provides information for educational purposes only and should not be considered legal or financial advice.
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.