Kimwolf Botnet Exploits Badbox 2.0: A Global Network Under Threat
A significant cybersecurity development has emerged, revealing that the operators of the Kimwolf botnet – a disruptive force infecting over two million devices – have reportedly gained unauthorized access to the control panel of Badbox 2.0. This vast botnet, primarily impacting Android TV streaming boxes, poses a substantial threat to user privacy and network security. Both the FBI and Google are actively investigating the individuals behind Badbox 2.0, and this latest development offers a crucial lead in their pursuit.
The Kimwolf botnet’s unique and invasive spread methods were detailed in our earlier report, “The Kimwolf Botnet is Stalking Your Local Network,” which highlighted the prevalence of compromised, unofficial Android TV boxes often marketed for unlimited access to pirated content. Our January 8th analysis, “Who Benefitted from the Aisuru and Kimwolf Botnets?” identified individuals known as “Dort” and “Snow” as key administrators of Kimwolf. Now, a source close to these individuals has provided evidence – a screenshot of the Badbox 2.0 control panel – suggesting a direct link between the two botnets.
The control panel for the Badbox 2.0 botnet lists authorized users and their email addresses.
The History of Badbox and its Expanding Reach
Badbox’s origins predate the rise of Kimwolf, with Google initiating legal action in July 2025 against 25 unidentified defendants accused of operating Badbox 2.0. The lawsuit, available here (PDF), described a botnet exceeding ten million compromised Android devices engaged in widespread advertising fraud. Google’s investigation revealed that Badbox 2.0 compromises devices both before purchase and through malicious app downloads from unofficial marketplaces.
This legal action followed a June 2025 advisory from the FBI, warning of cybercriminals exploiting vulnerabilities to gain unauthorized access to home networks. The FBI detailed tactics involving pre-installed malware or malicious applications downloaded during device setup. Badbox 2.0 emerged after the disruption of the original Badbox campaign in 2024, which initially targeted Android devices compromised with backdoor malware prior to sale.
Initial skepticism regarding the Kimwolf botmasters’ alleged access to Badbox 2.0 was quickly dispelled upon closer examination of the email addresses visible in the leaked screenshot. The investigation revealed a network of connections pointing to individuals and companies based in China.
Uncovering the Connections: Chen Daihai and Zhu Zhiyu
An online search revealed that the email address [email protected], associated with the user “Chen” in the screenshot, is linked to several China-based technology firms, including Beijing Hong Dake Wang Science & Technology Co Ltd, Beijing Hengchuang Vision Mobile Media Technology Co. Ltd, and Moxin Beijing Science and Technology Co. Ltd. The website for Beijing Hong Dake Wang Science, asmeisvip[.]net, was flagged in a March 2025 report by HUMAN Security as being associated with the distribution and management of Badbox 2.0. Similarly, moyix[.]com, linked to Beijing Hengchuang Vision Mobile, also appeared on HUMAN Security’s list.
Further investigation using Constella Intelligence revealed that the owner of [email protected] previously used the password “cdh76111,” a password also associated with the email addresses [email protected] and [email protected]. Constella data showed [email protected] registered an account on jd.com under the name “陈代海” (Chen Daihai). DomainTools.com confirmed Chen Daihai’s presence in the original registration records for moyix[.]com, alongside the email address cathead@astrolink[.]cn.
Astrolink[.]cn, also identified as a Badbox 2.0 domain by HUMAN Security, was found to be registered using cathead@astrolink[.]cn, which was linked to over a dozen domains, including vmud[.]net. A cached version of astrolink[.]cn from 2009 identifies the company as Beijing Astrolink Wireless Digital Technology Co. Ltd, listing Chen Daihai and Zhu Zhiyu as key personnel, with email addresses xavier@astrolink[.]cn and cathead@astrolink[.]cn respectively.
The user “Mr.Zhu” in the Badbox 2.0 panel used the email address [email protected], which Constella linked to a jd.com account registered in the name of Zhu Zhiyu. This account shared a password with [email protected], the original registrant of astrolink[.]cn.
Tracing the “Admin” Account to Huang Guilin
The first account listed in the Badbox 2.0 panel, “admin,” registered in November 2020, used the email address [email protected]. DomainTools connected this email to the domain guilincloud[.]cn and the registrant name Huang Guilin. Constella revealed a connection to the China phone number 18681627767, linked to a Microsoft profile under the name Guilin Huang (桂林 黄), and a Weibo account under the username “h_guilin.”
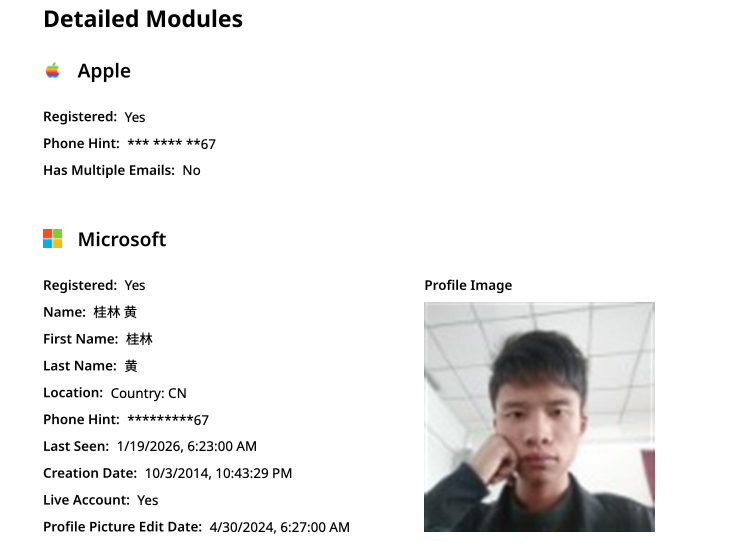
Public information associated with Guilin Huang’s Microsoft account.
While the remaining three users in the Badbox 2.0 panel were also linked to individuals in China, no apparent connection was found between them and Chen Daihai or Zhu Zhiyu. Attempts to contact these individuals for comment were unsuccessful.
The implications of Kimwolf’s access to Badbox 2.0 are significant. Kimwolf’s ability to bypass traditional proxy restrictions by directly loading malware onto compromised TV boxes represents a substantial escalation in their capabilities. Research from Synthient highlights the vulnerability of residential proxy services, which Kimwolf previously exploited to probe and compromise local networks. With direct access to Badbox 2.0, these vulnerabilities become less critical, allowing Kimwolf to maintain its reach even as proxy providers implement security measures.
Do you think the scale of this botnet is truly understood by the average consumer? What steps can individuals take to protect their home networks from these types of threats?
Frequently Asked Questions About Kimwolf and Badbox 2.0
What is the Kimwolf botnet and why is it dangerous?
The Kimwolf botnet is a network of over two million compromised devices used for malicious purposes. It’s dangerous because it can be used to launch attacks, steal data, and disrupt online services.
How does the Badbox 2.0 botnet compromise Android TV boxes?
Badbox 2.0 compromises Android TV boxes through pre-installed malware or malicious apps downloaded from unofficial marketplaces, often targeting devices offering access to pirated content.
What is the connection between Kimwolf and Badbox 2.0?
Recent evidence suggests that the operators of the Kimwolf botnet have gained unauthorized access to the Badbox 2.0 control panel, allowing them to directly distribute malware to compromised devices.
How can I protect my Android TV box from being infected by Badbox 2.0?
Avoid installing apps from unofficial sources, keep your device’s software updated, and consider using a reputable security app.
What steps are being taken to combat the Kimwolf and Badbox 2.0 threats?
The FBI and Google are actively investigating the individuals behind these botnets. Proxy providers are also working to patch vulnerabilities that Kimwolf previously exploited.
Is my home network at risk if I use an Android TV box?
Yes, if your Android TV box is compromised by Badbox 2.0 or other malware, your home network could be at risk. It’s crucial to take preventative measures to secure your devices.
This investigation underscores the evolving sophistication of cyber threats and the importance of vigilance in protecting your digital life. What further steps do you believe tech companies and law enforcement should take to address these emerging threats?
Disclaimer: This article provides information for educational purposes only and should not be considered legal or financial advice. Always consult with a qualified professional for specific guidance.
Share this article with your friends and family to help raise awareness about these critical security threats. Join the conversation and share your thoughts in the comments below!
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.

