The Looming Digital Cliff: How Expiring Certificates and Software Vulnerabilities Signal a New Era of Systemic Risk
Over 30% of all Windows devices globally could become inoperable within the next year, not due to hardware failure, but a silent, creeping expiration of a critical security certificate. This isn’t a hypothetical threat; it’s a ticking time bomb set to detonate in June 2026, and it’s symptomatic of a larger, more concerning trend: the increasing fragility of our digital infrastructure. The recent discovery of vulnerabilities, even in seemingly innocuous tools like Windows Notepad, further underscores this systemic risk.
The Secure Boot Certificate Crisis: A Deep Dive
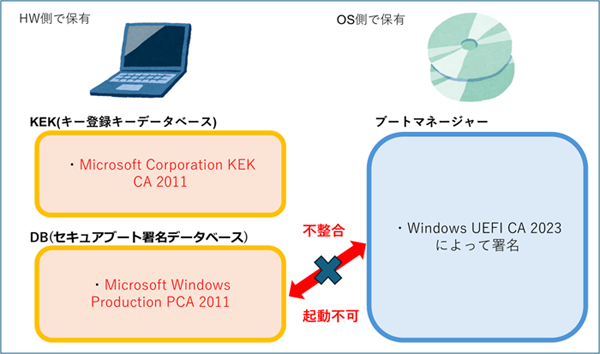
The impending expiration of the Windows secure boot certificate, first highlighted by PC Watch and ITmedia, is a significant issue. Secure Boot, a security standard developed by the Unified Extensible Firmware Interface (UEFI) Forum, helps ensure that only trusted software can boot on a device. Without a valid certificate, devices may refuse to start, effectively rendering them useless. Microsoft’s February update (KB5077181) is a crucial first step, but it’s not a complete solution. Many older systems, particularly those running older versions of Windows, may require manual intervention, and a significant portion of users are likely unaware of the looming problem. The core issue isn’t just the certificate itself, but the complexity of updating firmware across a vast and diverse ecosystem of hardware.
Beyond Secure Boot: A Cascade of Vulnerabilities
The secure boot issue isn’t happening in a vacuum. Recent reports from ScanNetSecurity, Yahoo! News, XenoSpectrum, and GIGAZINE detail a surge in discovered vulnerabilities, including a remote code execution flaw in Windows Notepad. While seemingly minor, this highlights a disturbing trend: even core system components are susceptible to attack. The speed at which vulnerabilities are being discovered and exploited is accelerating, outpacing the ability of security teams to patch them effectively. This is partly due to the increasing complexity of software, the proliferation of third-party libraries, and the rise of sophisticated attack vectors.
The AI Factor: A Double-Edged Sword
Microsoft’s attempt to integrate AI features into Notepad, while perhaps well-intentioned, ironically introduced a new vulnerability. This illustrates a critical point: the rush to incorporate AI into existing software is often prioritizing features over security. AI models themselves can be targets for attack, and their integration into core systems introduces new attack surfaces. The future will likely see a continued push for AI integration, but it must be accompanied by a corresponding investment in robust security measures. We’re entering an era where AI-powered attacks will become increasingly common, requiring AI-powered defenses.
The Rise of “Software Decay” and the Need for Proactive Management
These issues collectively point to a phenomenon we’re calling “software decay.” Software, unlike physical infrastructure, doesn’t simply wear out; it becomes increasingly vulnerable over time. Dependencies become outdated, security flaws are discovered, and compatibility issues arise. This requires a shift from reactive patching to proactive software lifecycle management. Organizations and individuals need to adopt strategies for regularly updating firmware, assessing vulnerability risks, and planning for eventual software obsolescence. This includes considering the total cost of ownership, not just the initial purchase price, and factoring in the ongoing costs of security maintenance.
The Implications for IoT and Embedded Systems
The challenges facing Windows are mirrored in the world of IoT and embedded systems. Millions of devices, from smart appliances to industrial control systems, rely on outdated software and vulnerable firmware. These devices often lack the resources for regular updates, making them prime targets for attackers. The potential consequences are far-reaching, ranging from privacy breaches to critical infrastructure failures. A standardized approach to security updates and a greater emphasis on secure-by-design principles are essential to mitigate these risks.
| Risk Factor | Impact | Mitigation Strategy |
|---|---|---|
| Expiring Secure Boot Certificates | Device Inoperability | Apply Microsoft Updates, Manual Firmware Updates |
| Software Vulnerabilities | Data Breaches, System Compromise | Regular Patching, Vulnerability Scanning |
| AI Integration Risks | New Attack Surfaces | Secure AI Development Practices, Robust Testing |
| IoT/Embedded System Vulnerabilities | Widespread System Failures | Standardized Updates, Secure-by-Design |
Frequently Asked Questions About Systemic Digital Risk
What can I do to protect my Windows PC from the secure boot certificate issue?
Ensure you have the latest Windows updates installed, including KB5077181. Check your device manufacturer’s website for specific firmware update instructions. If you have older hardware, you may need to manually update the firmware.
How can I stay ahead of emerging software vulnerabilities?
Enable automatic updates for your operating system and applications. Use a reputable antivirus and anti-malware program. Be cautious about clicking on links or downloading files from unknown sources.
What is the role of manufacturers in addressing software decay?
Manufacturers have a responsibility to provide long-term security support for their products, including regular updates and vulnerability patches. They should also adopt secure-by-design principles to minimize the risk of future vulnerabilities.
Will AI make cybersecurity more or less secure?
AI has the potential to both enhance and undermine cybersecurity. AI-powered tools can automate threat detection and response, but they can also be used to create more sophisticated attacks. The key is to develop and deploy AI responsibly, with a strong focus on security.
The convergence of expiring certificates, escalating vulnerabilities, and the complexities of AI integration paints a stark picture of the challenges ahead. Ignoring these warning signs is not an option. Proactive security management, a commitment to continuous updates, and a forward-looking approach to software lifecycle management are no longer best practices – they are essential for survival in the increasingly fragile digital landscape. What are your predictions for the future of digital security? Share your insights in the comments below!
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.