The Shadow War Expands: How Targeted Killings in Ukraine Signal a New Era of Hybrid Conflict
Over 80% of geopolitical instability now involves non-state actors and covert operations, a dramatic increase from just a decade ago. Recent revelations of a Russian-backed plot to assassinate prominent Ukrainians, including President Zelenskyy, alongside similar schemes targeting Moldovan officials, aren’t isolated incidents. They represent a dangerous escalation – a shift towards a more pervasive and insidious form of warfare that leverages deniable operations and targets leadership directly.
Beyond Traditional Warfare: The Rise of Paramilitary Influence Operations
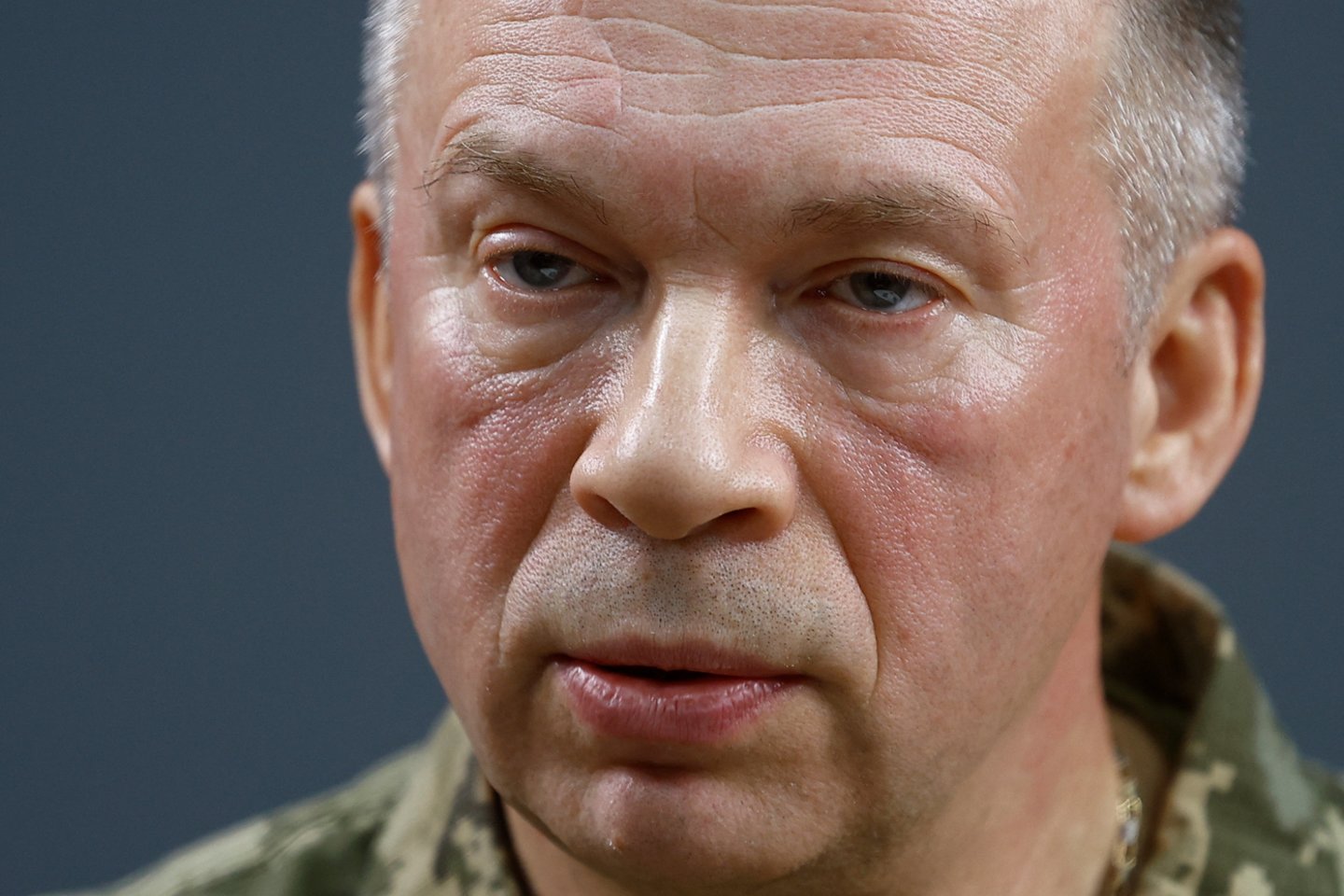
The coordinated nature of these assassination attempts, as reported by sources like Lrytas, Delfi, tv3.lt, 15min.lt, and CNN, points to a sophisticated network operating across borders. The fact that operatives disguised themselves as couriers highlights a key tactic: blending into everyday life to circumvent traditional security measures. This isn’t simply about eliminating individuals; it’s about sowing chaos, destabilizing governments, and eroding public trust. The Ukrainian Security Service’s (SBU) success in uncovering this network, as highlighted by Syrskyi as a pivotal achievement, is significant, but it’s also a warning. The scale of the operation suggests a broader, ongoing effort.
The Moldova Connection: A Regional Pattern of Destabilization
The simultaneous targeting of Ukrainian and Moldovan leaders is particularly concerning. Moldova, already grappling with internal political tensions and Russian influence, is increasingly vulnerable to such destabilization efforts. The collaboration between Ukrainian and Moldovan intelligence agencies in exposing this plot demonstrates a growing awareness of the interconnected nature of these threats. This regional pattern suggests a deliberate strategy to weaken countries perceived as aligning with the West.
The Technological Arms Race: AI and the Future of Assassination
While the current methods rely on human operatives, the future of these types of operations will undoubtedly be shaped by advancements in artificial intelligence. **AI-powered surveillance**, facial recognition, and predictive policing could be used to identify and track potential targets with unprecedented accuracy. Furthermore, the development of autonomous drones and robotic systems raises the specter of automated assassination capabilities. The ethical and security implications are profound. We are entering an era where the line between intelligence gathering and targeted elimination is becoming increasingly blurred.
Deepfakes and Disinformation: Amplifying the Impact
Even if an assassination attempt fails, the accompanying disinformation campaign can be devastating. Deepfake technology can be used to create convincing but fabricated evidence, blaming rivals or inciting public unrest. The spread of such misinformation through social media can rapidly erode trust in institutions and exacerbate existing divisions. The ability to manipulate public perception is becoming as important as the ability to physically eliminate targets.
The Implications for Global Security: A New Normal?
The events in Ukraine and Moldova are not isolated incidents. They are indicative of a broader trend towards increased geopolitical instability and the weaponization of non-state actors. Governments around the world must adapt to this new reality by investing in enhanced intelligence gathering, cybersecurity defenses, and counter-disinformation strategies. International cooperation is also crucial to sharing information and coordinating responses to these evolving threats. The traditional tools of statecraft are no longer sufficient to address the challenges posed by this new era of hybrid conflict.
The success of these operations hinges on exploiting vulnerabilities in security protocols and leveraging the anonymity afforded by modern technology. Expect to see a continued focus on infiltrating critical infrastructure, compromising communication networks, and exploiting social engineering techniques. The future of conflict will be fought not only on battlefields but also in the digital realm and within the shadows of our societies.
Frequently Asked Questions About Targeted Killings and Hybrid Warfare
What are the biggest challenges in countering these types of operations?
The primary challenges lie in attribution – definitively proving the involvement of state actors – and the difficulty of detecting and disrupting covert operations. The use of proxies and deniable assets makes it harder to hold perpetrators accountable.
How can governments protect high-profile individuals from assassination attempts?
Enhanced security protocols, including advanced surveillance, threat assessment, and counter-surveillance measures, are essential. However, the most effective defense is often proactive intelligence gathering to identify and neutralize threats before they materialize.
What role does technology play in both enabling and countering these threats?
Technology is a double-edged sword. It enables adversaries to carry out sophisticated operations with greater efficiency and anonymity, but it also provides tools for detection, analysis, and defense. The key is to stay ahead of the curve and leverage technological advancements to protect against emerging threats.
The unfolding situation in Ukraine and Moldova serves as a stark reminder that the world is becoming a more dangerous place. The era of traditional warfare is giving way to a new era of hybrid conflict, characterized by covert operations, disinformation campaigns, and the targeting of leadership. Staying informed, adapting to evolving threats, and fostering international cooperation are essential to navigating this complex and uncertain landscape.
What are your predictions for the future of state-sponsored assassination attempts? Share your insights in the comments below!
Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.