123
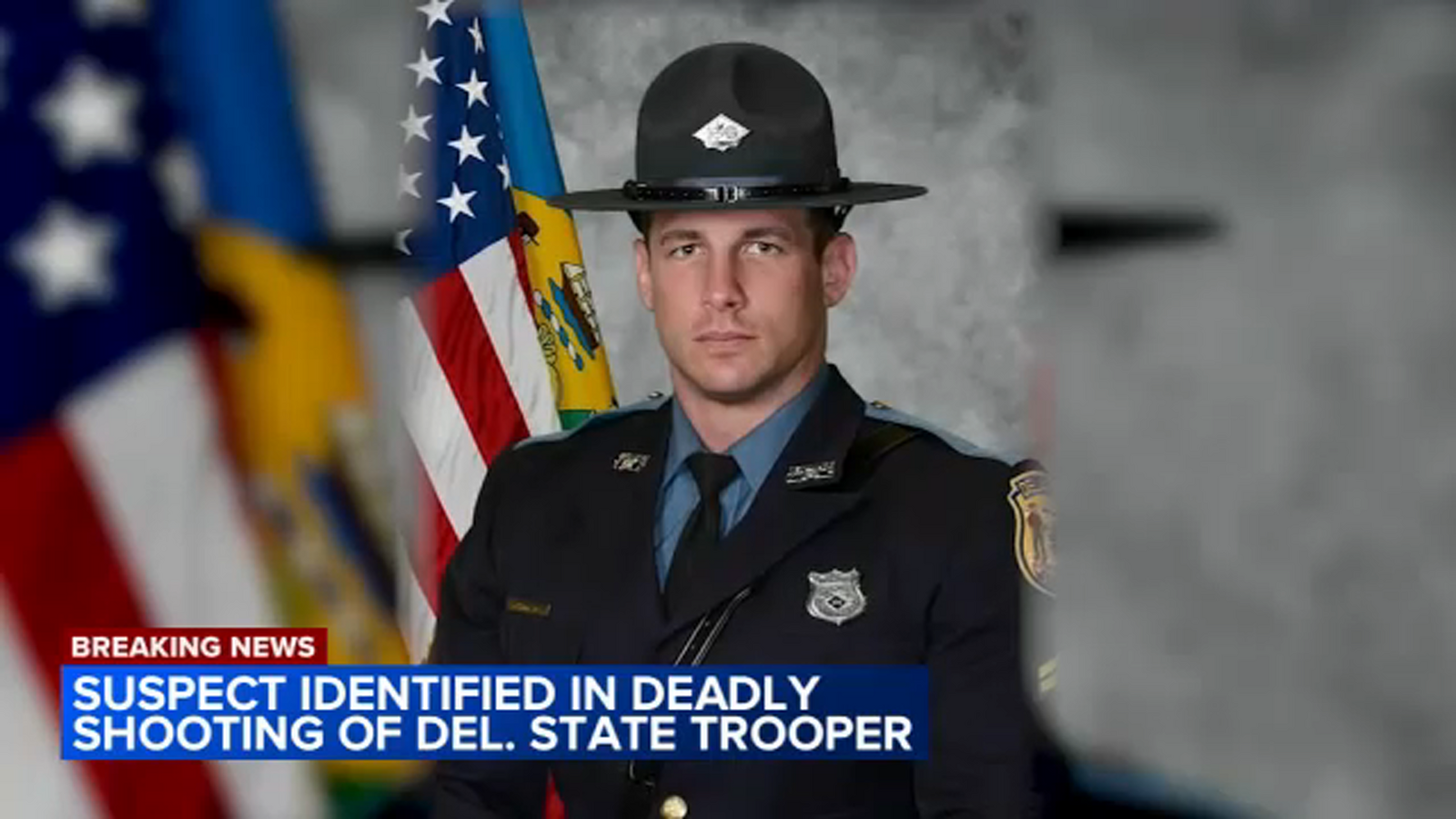
<p>Nearly 30,000 Americans are injured by firearms annually while on the job, a statistic that often obscures the disproportionate risk faced by those in public-facing roles. The recent, heartbreaking death of Delaware State Police Cpl. Matthew “Ty” Snook at a Wilmington DMV facility isn’t an isolated incident, but a stark symptom of a broader, escalating threat to public servants. This event, where the suspect reportedly allowed customers to leave before engaging officers, forces a critical re-evaluation of security protocols and a proactive look at the future of safety in civilian government spaces.</p>
<h2>Beyond Metal Detectors: The Evolving Landscape of Public Safety</h2>
<p>Traditional security measures – metal detectors, security guards – are increasingly proving insufficient against determined attackers. The Delaware shooting underscores a disturbing trend: attackers are often willing to prioritize maximizing casualties among law enforcement, strategically positioning themselves and exploiting vulnerabilities in response times. The suspect’s calculated actions, allowing civilians to depart before confronting officers, suggest a deliberate attempt to create a more focused and lethal engagement. This isn’t simply about preventing entry; it’s about mitigating the <em>tactical advantage</em> an attacker seeks.</p>
<h3>The Rise of “Soft Target” Awareness and Active Shooter Protocols</h3>
<p>The term “soft target” has become tragically commonplace, referring to locations with limited security and a high concentration of people. DMVs, courthouses, and social service offices fall squarely into this category. While active shooter drills have become more frequent, their effectiveness hinges on consistent training, rapid response capabilities, and a culture of vigilance. However, training alone isn’t enough. We need to move beyond reactive measures and embrace proactive threat assessment and mitigation strategies.</p>
<h2>Technological Innovations for Enhanced Security</h2>
<p>Fortunately, advancements in technology offer promising avenues for bolstering security in these vulnerable locations. **Artificial intelligence (AI)**-powered surveillance systems, for example, can analyze real-time video feeds to detect anomalous behavior – unusual movements, concealed weapons, or suspicious loitering – and alert security personnel *before* an incident occurs. This isn’t about replacing human oversight, but augmenting it with a powerful analytical tool.</p>
<p>Other emerging technologies include:</p>
<ul>
<li><strong>Behavioral Analysis Software:</strong> Identifying pre-attack indicators based on patterns of behavior.</li>
<li><strong>Advanced Access Control Systems:</strong> Utilizing biometrics and multi-factor authentication to restrict access to sensitive areas.</li>
<li><strong>Drone-Based Surveillance:</strong> Providing rapid aerial assessment of potential threats and situational awareness.</li>
<li><strong>Enhanced Communication Systems:</strong> Ensuring seamless communication between security personnel, law enforcement, and first responders.</li>
</ul>
<h3>The Data Privacy Dilemma</h3>
<p>The implementation of these technologies, however, raises legitimate concerns about data privacy and civil liberties. Striking a balance between security and individual rights is paramount. Transparent policies, robust data encryption, and strict oversight mechanisms are essential to ensure that these technologies are used responsibly and ethically.</p>
<h2>The Human Factor: Supporting Frontline Workers</h2>
<p>Technology alone cannot solve this problem. The mental and emotional toll on frontline workers – those who interact directly with the public – is immense. Providing comprehensive psychological support, stress management training, and peer support networks is crucial. These individuals are often the first line of defense, and their well-being is inextricably linked to the safety of the public.</p>
<p>Furthermore, empowering employees to report suspicious activity without fear of retribution is vital. A culture of open communication and proactive threat reporting can significantly enhance situational awareness and prevent potential incidents.</p>
<table>
<thead>
<tr>
<th>Security Measure</th>
<th>Current Adoption Rate</th>
<th>Projected Adoption Rate (2028)</th>
</tr>
</thead>
<tbody>
<tr>
<td>AI-Powered Surveillance</td>
<td>15%</td>
<td>60%</td>
</tr>
<tr>
<td>Behavioral Analysis Software</td>
<td>8%</td>
<td>45%</td>
</tr>
<tr>
<td>Enhanced Access Control</td>
<td>30%</td>
<td>75%</td>
</tr>
</tbody>
</table>
<p>The death of Cpl. Snook serves as a tragic reminder of the risks faced by those who dedicate their lives to public service. Addressing this escalating threat requires a multi-faceted approach – one that combines technological innovation, proactive security protocols, and a unwavering commitment to supporting the well-being of frontline workers. The future of public safety depends on our ability to learn from these tragedies and build a more secure and resilient environment for all.</p>
<h2>Frequently Asked Questions About Public Servant Safety</h2>
<h3>What are the biggest challenges in securing public-facing government facilities?</h3>
<p>The primary challenges include balancing security with accessibility, the difficulty of detecting concealed threats, and the need to address the psychological impact on frontline workers.</p>
<h3>How can AI be used to improve security without infringing on privacy?</h3>
<p>AI can be used to analyze data anonymously and identify patterns of suspicious behavior without collecting personally identifiable information. Transparent policies and strict data encryption are also crucial.</p>
<h3>What role does employee training play in preventing attacks?</h3>
<p>Employee training is essential for recognizing and reporting suspicious activity, understanding active shooter protocols, and fostering a culture of vigilance.</p>
<h3>What is the cost of implementing these new security measures?</h3>
<p>The cost varies depending on the specific technologies and protocols implemented. However, the cost of inaction – in terms of lives lost and societal disruption – is far greater.</p>
<p>What are your predictions for the future of security in public service locations? Share your insights in the comments below!</p>
<script>
// JSON-LD Schema
const schema = `
{
"@context": "https://schema.org",
"@type": "NewsArticle",
"headline": "The Rising Threat to Public Servants: Reimagining Security in Civilian-Facing Government Facilities",
"datePublished": "2025-06-24T09:06:26Z",
"dateModified": "2025-06-24T09:06:26Z",
"author": {
"@type": "Person",
"name": "Archyworldys Staff"
},
"publisher": {
"@type": "Organization",
"name": "Archyworldys",
"url": "https://www.archyworldys.com"
},
"description": "The tragic shooting of Cpl. Snook highlights a growing vulnerability in public service locations. This article explores the evolving security landscape and potential solutions for protecting frontline workers."
}
{
"@context": "https://schema.org",
"@type": "FAQPage",
"mainEntity": [
{
"@type": "Question",
"name": "What are the biggest challenges in securing public-facing government facilities?",
"acceptedAnswer": {
"@type": "Answer",
"text": "The primary challenges include balancing security with accessibility, the difficulty of detecting concealed threats, and the need to address the psychological impact on frontline workers."
}
},
{
"@type": "Question",
"name": "How can AI be used to improve security without infringing on privacy?",
"acceptedAnswer": {
"@type": "Answer",
"text": "AI can be used to analyze data anonymously and identify patterns of suspicious behavior without collecting personally identifiable information. Transparent policies and strict data encryption are also crucial."
}
},
{
"@type": "Question",
"name": "What role does employee training play in preventing attacks?",
"acceptedAnswer": {
"@type": "Answer",
"text": "Employee training is essential for recognizing and reporting suspicious activity, understanding active shooter protocols, and fostering a culture of vigilance."
}
},
{
"@type": "Question",
"name": "What is the cost of implementing these new security measures?",
"acceptedAnswer": {
"@type": "Answer",
"text": "The cost varies depending on the specific technologies and protocols implemented. However, the cost of inaction – in terms of lives lost and societal disruption – is far greater."
}
}
]
}
`;
document.body.insertAdjacentHTML('beforeend', '<script type="application/ld+json">' + schema + '</script>');
</script>Discover more from Archyworldys
Subscribe to get the latest posts sent to your email.